Generate Random Aes 256 Key C
Posted : admin On 15.04.2020
Chilkat • HOME • Android™ • Classic ASP • C • C++ • C# • Mono C# • .NET Core C# • C# UWP/WinRT • DataFlex • Delphi ActiveX • Delphi DLL • Visual FoxPro • Java • Lianja • MFC • Objective-C • Perl • PHP ActiveX • PHP Extension • PowerBuilder • PowerShell • PureBasic • CkPython • Chilkat2-Python • Ruby • SQL Server • Swift 2 • Swift 3/4 • Tcl • Unicode C • Unicode C++ • Visual Basic 6.0 • VB.NET • VB.NET UWP/WinRT • VBScript • Xojo Plugin • Node.js • Excel • Go
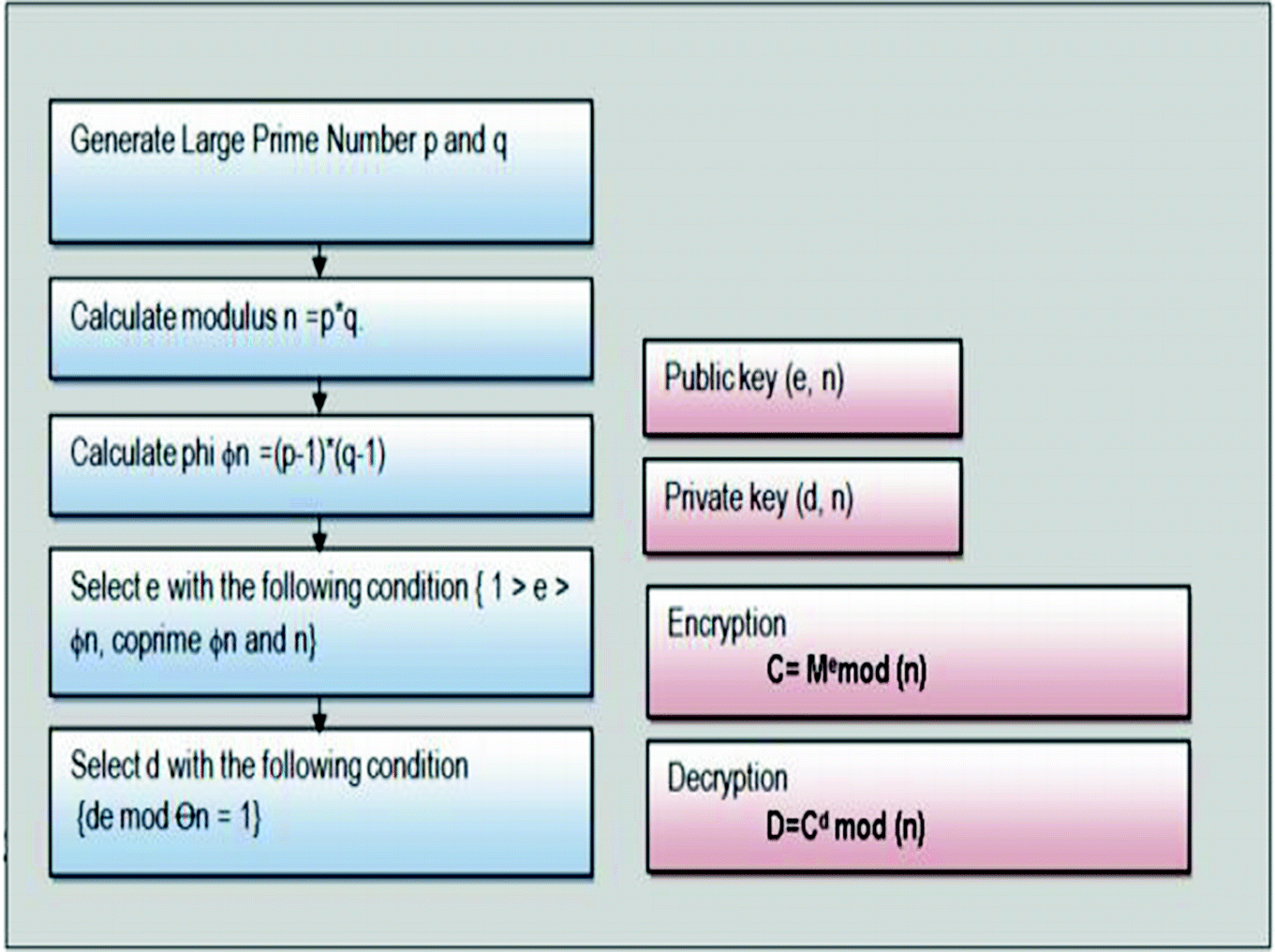
AES Key Generator Devon 2019-04-27T15:14:21-07:00 Below is a Base64 Encoded AES-256 key which was been generated using the secure javax KeyGenerator. This key will work perfectly with any of the AES encryption code elsewhere on my site, and probably most of yours as well. Static IV and random keys using aes-256-cbc. Ask Question. Are there any security risks in using a static IV if I generate a new random KEY for each set of data to. I'm trying to create a strong key for encrypting some data using AES-256 for fun and practice. For my own practice, I want to make this as strong as possible, I don't care how long it takes to complete. I got some advice from 1Password white paper and therefore I want to use 2 secret keys. The master password and a random generated 32-byte string. Ways to generate symmetric and asymmetric keys. Seed enough entropy to generate more secure random number. 16 myaes.key AES-256 expects a key of 256 bit, 32. Generating Symmetric Private Key In C# and.NET. Major symmetric algorithms are AES, DES, RC2, Rijndael, and TripleDES. The GenerateKey and GenerateIV methods return the private secret key and initialization vector.
256 bit encryption. SSH keys grant access, and fall under this requirement. A widely used SSH key management tool for OpenSSH is.Practically all cybersecurity require managing who can access what.
| Discusses symmetric encryption key generation techniques for block encryption algorithms such as AES, Blowfish, and Twofish, or for other algorithms such as ChaCha20.
| |||||
© 2000-2020 Chilkat Software, Inc. License key generator software free download free. All Rights Reserved.
Static IV and random keys using aes-256-cbc. Ask Question. Are there any security risks in using a static IV if I generate a new random KEY for each set of data to encrypt? If I understand correctly what the purpose of the IV is in Cipher-block chaining mode of operation, there is no issue in doing things like this. Am I missing something?