256 Bit Encryption Key Generator
Posted : admin On 09.04.2020- Aes 128 Key Generator
- Encryption Key Generator 128 Bit
- Aes 256 Encryption Key Generator
- 256 Bit Encryption Key Generator Free
- 128 Bit Encryption Key Generator
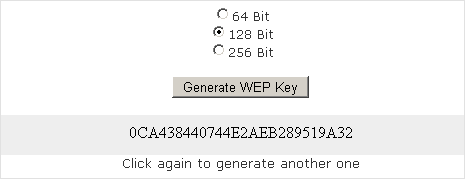
Generate a SHA-256 hash with this free online encryption tool. To create a SHA-256 checksum of your file, use the upload feature. To further enhance the security of you encrypted hash you can use a shared key. Sha256 converter. So, although this key has 256 bits in it, the security is actually only 128 bits, because each character has only 4 bit in a Hex-encoded string. So using only half of the key/iv provides the same encryption result in CryptoJS. Random Key Generator, a powerful password and key generator that can generate Memorable Password, Strong Password, Fort Knox Password, CodeIgniter Encryption Key, 160-bit WPA Key, 504-bit WPA Key, 64-bit WEP Key, 128-bit WEP Key, 152-bit WEP Key, 256-bit WEP Key. You can use this generator to secure any service, application or device. AES provides 128 bit, 192 bit and 256 bit of secret key size for encryption. Things to remember here is if you are selecting 128 bits for encryption, then the secret key must be of 16 bits long and 24 and 32 bits for 192 and 256 bits of key size. AES was designed to be efficient in both hardware and software, and supports a block length of 128 bits and key lengths of 128, 192, and 256 bits. How secure is AES encryption algorithm? AES encryption is used by U.S. For securing sensitive but unclassified material, so we can say it is enough secure.
-->Creating and managing keys is an important part of the cryptographic process. Symmetric algorithms require the creation of a key and an initialization vector (IV). The key must be kept secret from anyone who should not decrypt your data. The IV does not have to be secret, but should be changed for each session. Asymmetric algorithms require the creation of a public key and a private key. The public key can be made public to anyone, while the private key must known only by the party who will decrypt the data encrypted with the public key. This section describes how to generate and manage keys for both symmetric and asymmetric algorithms.
This is great for encryption, but most private keys use a Private Key in the PEM format seen below. Rsa private and public key generator javascript library. Other InformationThis library heavily utilizes the wonderful work of Tom Wu found at.This jsbn library was written using the raw variables to perform encryption.
Symmetric Keys
The symmetric encryption classes supplied by the .NET Framework require a key and a new initialization vector (IV) to encrypt and decrypt data. Whenever you create a new instance of one of the managed symmetric cryptographic classes using the parameterless constructor, a new key and IV are automatically created. Anyone that you allow to decrypt your data must possess the same key and IV and use the same algorithm. Generally, a new key and IV should be created for every session, and neither the key nor IV should be stored for use in a later session.
To communicate a symmetric key and IV to a remote party, you would usually encrypt the symmetric key by using asymmetric encryption. Sending the key across an insecure network without encrypting it is unsafe, because anyone who intercepts the key and IV can then decrypt your data. For more information about exchanging data by using encryption, see Creating a Cryptographic Scheme.
The following example shows the creation of a new instance of the TripleDESCryptoServiceProvider class that implements the TripleDES algorithm.
When the previous code is executed, a new key and IV are generated and placed in the Key and IV properties, respectively.
Sometimes you might need to generate multiple keys. In this situation, you can create a new instance of a class that implements a symmetric algorithm and then create a new key and IV by calling the GenerateKey and GenerateIV methods. The following code example illustrates how to create new keys and IVs after a new instance of the symmetric cryptographic class has been made.
Aes 128 Key Generator
When the previous code is executed, a key and IV are generated when the new instance of TripleDESCryptoServiceProvider is made. Another key and IV are created when the GenerateKey and GenerateIV methods are called.
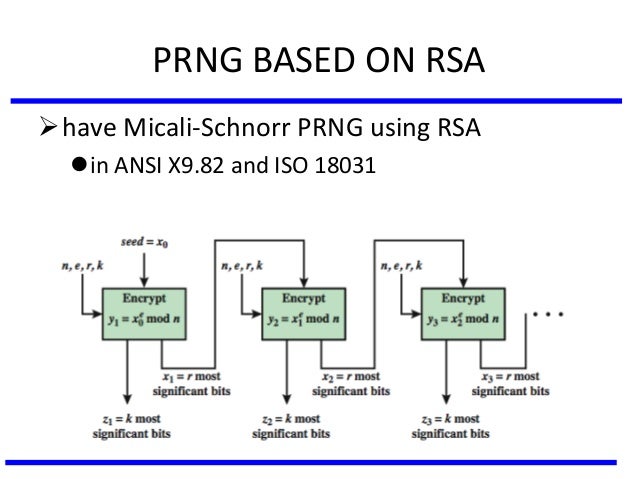
Asymmetric Keys
The .NET Framework provides the RSACryptoServiceProvider and DSACryptoServiceProvider classes for asymmetric encryption. These classes create a public/private key pair when you use the parameterless constructor to create a new instance. Asymmetric keys can be either stored for use in multiple sessions or generated for one session only. While the public key can be made generally available, the private key should be closely guarded.
Encryption Key Generator 128 Bit
A public/private key pair is generated whenever a new instance of an asymmetric algorithm class is created. After a new instance of the class is created, the key information can be extracted using one of two methods:
The ToXmlString method, which returns an XML representation of the key information.
The ExportParameters method, which returns an RSAParameters structure that holds the key information.
Gen Y - They are better educated, more techno-savvy, and quicker to adapt then those who have come before them, they refuse to blindly follow traditio. Some people also include children born in the early 2000s. The Millennial Generation is also known as Generation Y, because it comes after Generation X — those people between the early 1960s and the 1980s. The publication Ad Age was one of the first to coin the term 'Generation Y. Jun 15, 2015 7 Key Characteristics of Gen-Y June 15, 2015 Pat McGovern Education. When it comes to the Millennial generation, there is no one size fits all approach. This is a big, diverse group and often times hard for marketing and admissions teams to understand. Here are some of the main characteristics to define Generation Y. Get to know them well as they will someday be heading up the businesses we are. Tech/Web Savvy: I’ll send you an email’. Generation Y were born into an emerging world of technology and have grown up surrounded by smart. Common Characteristics of Generation Y Professionals. WHO ARE GENERATION Y PROFESSIONALS? According to the U.S Census Bureau, Generation Y is comprised of people who were born between 1982 and 2000. GENERATION Y IS VERY TECH SAVVY. GEN ERATION Y PREFERS FLEXIBILITY. GENERATION Y IS AMBITIOUS AND. Key traits of generation y.
Both methods accept a Boolean value that indicates whether to return only the public key information or to return both the public-key and the private-key information. An RSACryptoServiceProvider class can be initialized to the value of an RSAParameters structure by using the ImportParameters method.
Aes 256 Encryption Key Generator
Asymmetric private keys should never be stored verbatim or in plain text on the local computer. If you need to store a private key, you should use a key container. For more on how to store a private key in a key container, see How to: Store Asymmetric Keys in a Key Container.
256 Bit Encryption Key Generator Free
The following code example creates a new instance of the RSACryptoServiceProvider class, creating a public/private key pair, and saves the public key information to an RSAParameters structure.